XI Commandment: Do not covet thy neighbour’s data. Individuals are responsible for 82% of data breaches. This clearly puts the person at the center of the fraudulent activity known as Social engineering. The human element is therefore the key to data breaches.
We often hear about how (personal) data is the new oil. Large digital companies acquire and manage user data on a daily basis, which mainly concerns internet activities. What happens if those who acquire these huge flows of data and information are instead subjects whose intentions are not only unknown, but also beyond the control of the regulatory framework?
For several years, institutional protagonists at national and international level have been studying the problem of data and how they are shared above all on the internet, in particular to ensure that those concerned can exercise maximum control.
The so-called Social engineering consists of a series of manipulation techniques aimed at exploiting human error in order to obtain confidential information, access credentials or physical/digital values. In the field of cybercrime, these “human hacking” techniques are designed to entice users to provide their data, spread malware or allow access to password-protected systems. These are real attacks that can take place online, in person or through other methods.
Social engineering scams are based on the way people think and act, and for this reason they try to manipulate user behavior. Once defined what can actually leverage on the user, the criminal will try to exploit it to his advantage. Furthermore, hackers often try to take advantage by exploiting the lack of knowledge about new technologies. Thanks to the speed with which these new technologies spread, many consumers and professionals of the sector cannot keep up with the threats inherent in these innovations. Furthermore, users often do not understand the importance and potential that their personal data have, underestimating, for example, the importance of their telephone number. Those who exploit social engineering tend to pursue objectives of sabotage or theft.
But how does it work?
Most of the activities involving social engineering take place on the basis of communication between the attacker and the victim; the criminal seeks to extort information from the victim, rather than trying to get it by brute force methods.
No reason to go hide out in an underground bunker, surrounded by analog devices, though! Technology is a resource and embracing change opens the way to new and exciting possibilities, keeping in mind a few simple precautions:
- Be wary of unsolicited emails and phone calls.
- Do not share personal information on untrusted sites and, in general, online.
- Do not download apps and programs from unverified sources.
- Check the URLs of websites to visit.
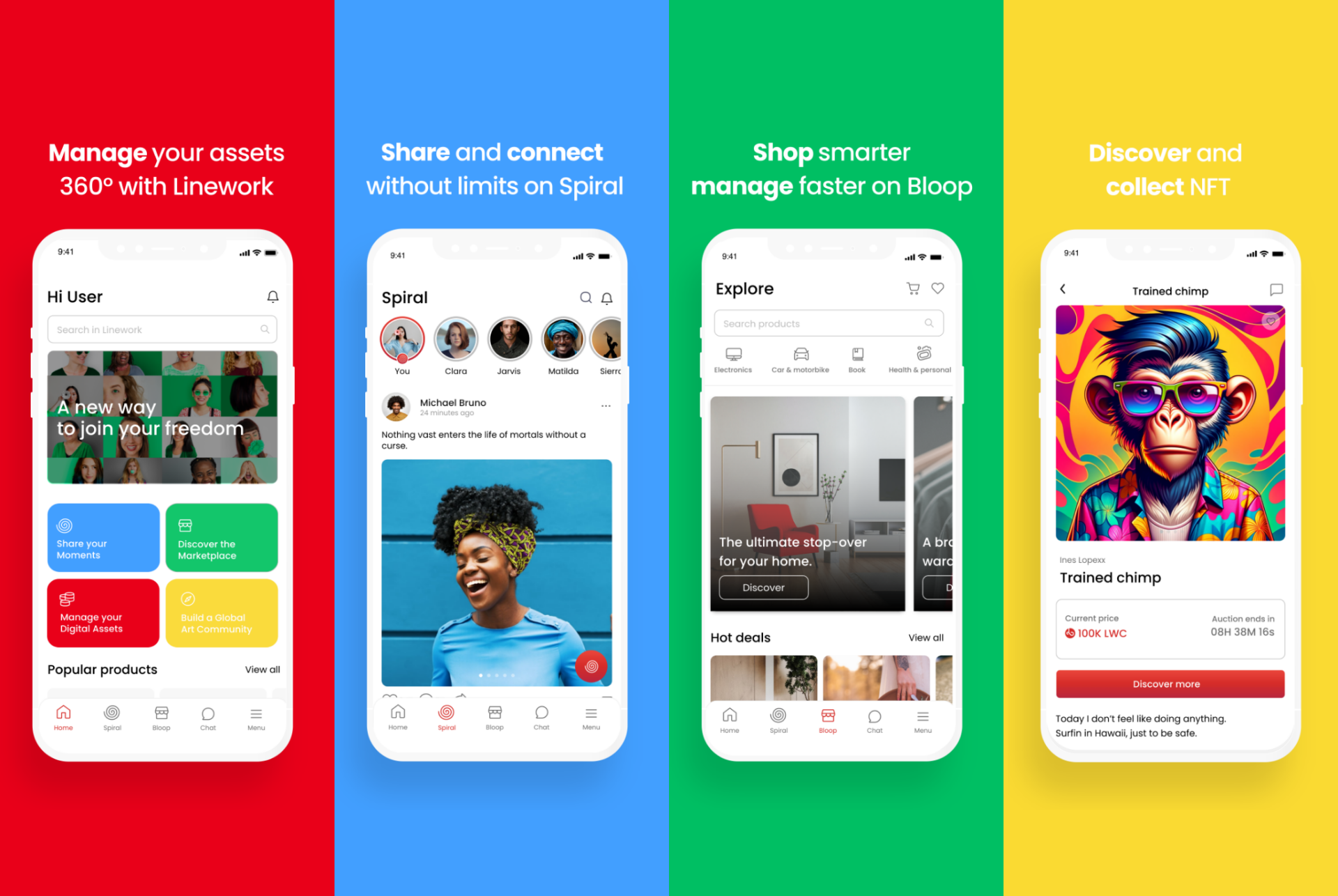
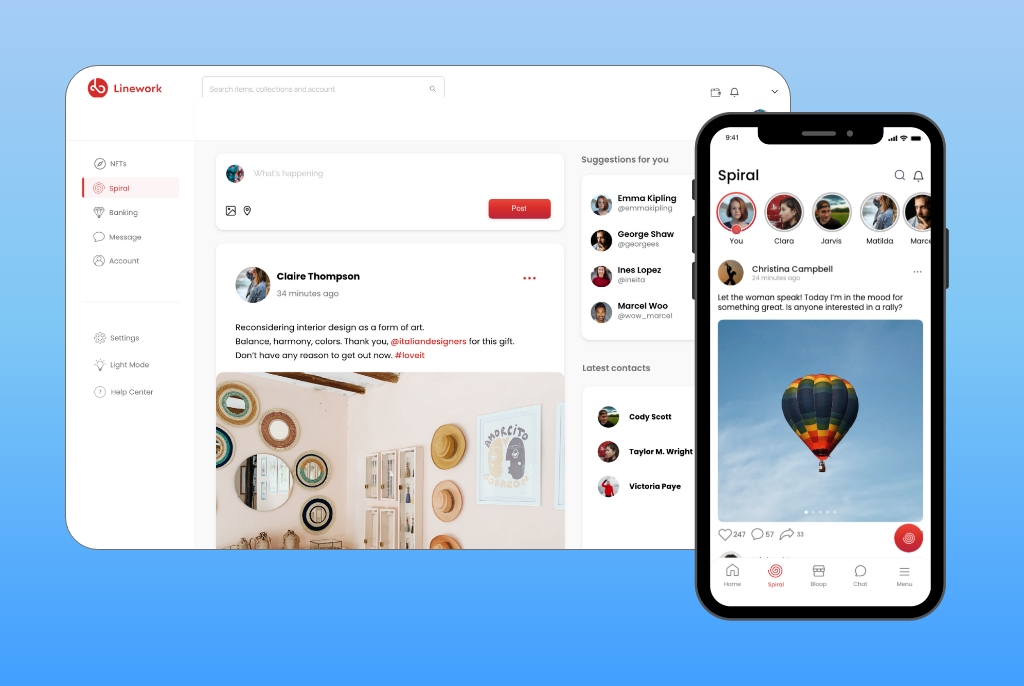
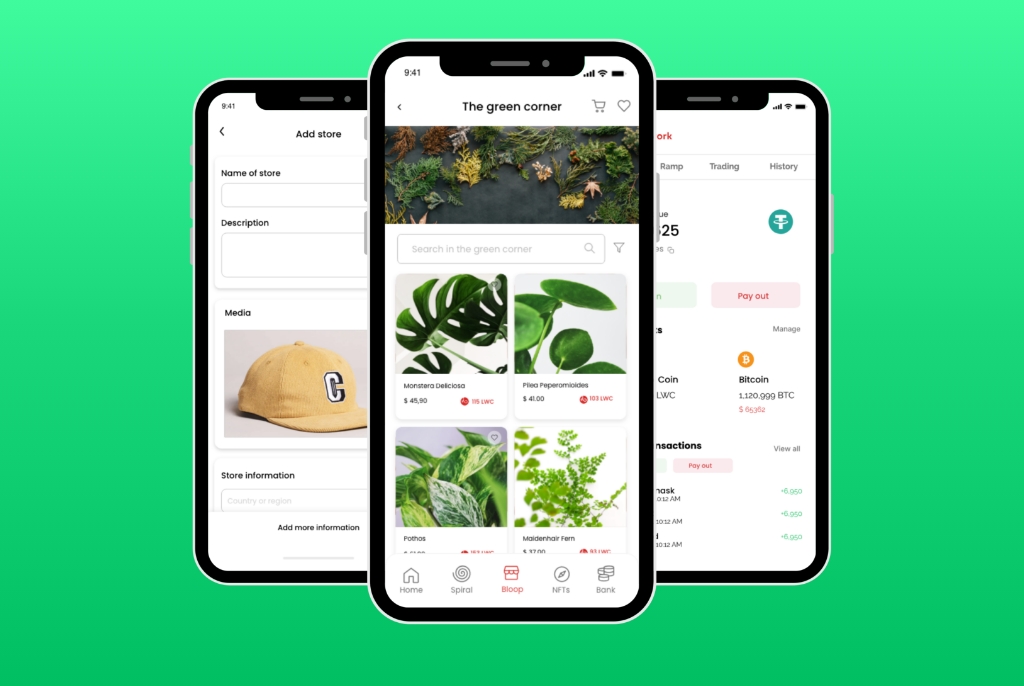
Linework is very sensitive to the safety of its users who, in order to make the most of the ecosystem offered by the application and manage their digital assets at 360°, must be protected by the best security measures imaginable, especially to guarantee their privacy. Linework processes its users’ data in full compliance with the rules established by the GDPR, so much so that it has decided to spontaneously appoint a DPO (Data Protection Officer), who is a professional technical figure who acts independently against the company, whose purpose is to check that the data controller acts in full compliance with the GDPR. Nothing different from what we were told as children: don’t talk to strangers, don’t accept candy from anyone, tell me where you go, tell me who you go with. Same principle, different means! Once these few rules are taken into account, the sea of technology becomes calm and safe… Ready to let us explore new horizons!